With Security 4X administrators can have the confidence that they plan, model, and test security migrations before implementing a large-scale change. With Security 4X administrators can carry out the following types of tasks which are virtually impossible without a purpose-built tool. They can: establish a baseline of current security settings in a centralized database; completely wipe away, rebuild, and migrate security from one geography, platform, and/or tier to another; have full logging and reporting regarding mass changes; and, maintain corporate audit standards simultaneously.
With Security 4X, any of the following types of security migrations are possible:
Administrators need the ability to make security changes on a user-by-user basis, but also need the ability to make large-scale, mass changes.
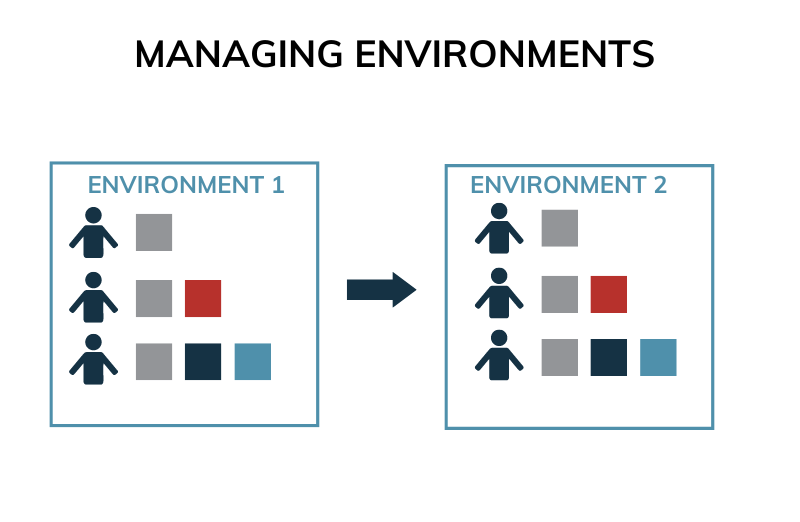
Moving security from one environment to another or to various geographic/departmental servers en masse is all part of Security 4X's design. Security 4X is designed to address mass changes that can only be reliably implemented through automation. This includes wiping an environment totally clean, redesigning the group/membership structure in a worksheet, importing the security changes into the Security 4X actions log, and mass implementing an entirely new structure.
Security 4X is designed in such a way that you can design security at the database level and implement it in your target platform when ready. It starts with a security export from your current platform, continues with developing the new security design in Security 4X, and then implementing it in your new platform. If you are moving from one security platform to another, Security 4X provides automation and reporting before, during, and after the migration. Security 4X supports these platforms: Apache Directory, Google Groups, HCL Domino, IBM Cognos, Microsoft Active Directory, NetIQ eDirectory, and Okta.
Security 4X provides security automation for all security transactions that are important to implementing enterprise security en masse. No more manual changes. All changes are implemented through governed processes.
Changes may be reversed via easy-to-implement scripting that can be mapped in Excel and then run through the Security 4X processing engine.
Security 4X provides tools that allow you to snapshot your entire environment so that you have an up to the minute baseline of security status.
Security 4X logs every change made to an environment. Every security change is logged by time, administrator, the type of security change being made, and precisely what was changed.
Security 4X provides 25+ standard security reports so that you have visibility into current state and historical changes.


