Many people use the term “data security” when they speak broadly about security and compliance. In reality, both security and compliance break down into several disciplines such as regulatory and corporate compliance, data security, content security, feature security, controls, traceability and more. Each has its own nuances and impacts how we authorize users in pursuit of the true role appropriate view. Read on to learn more.

Corporate and regulatory compliance regulations around the world are becoming more and more pervasive as we continue in the digital age. Applying frameworks, processes and internal controls is in hyper-growth globally. If your organization is concerned about data security, privacy, Information Access Management (IAM), Access Control, regulatory or corporate compliance then security governance with integrated auditing and intelligence reporting is at the center of how you manage, and govern business process compliance and IAM functions.
All too often, implementing security to align with compliance requirements is a tedious, cumbersome, and usually manual process. It relies on people rather than well-formed security policies that apply security changes automatically and without fail.
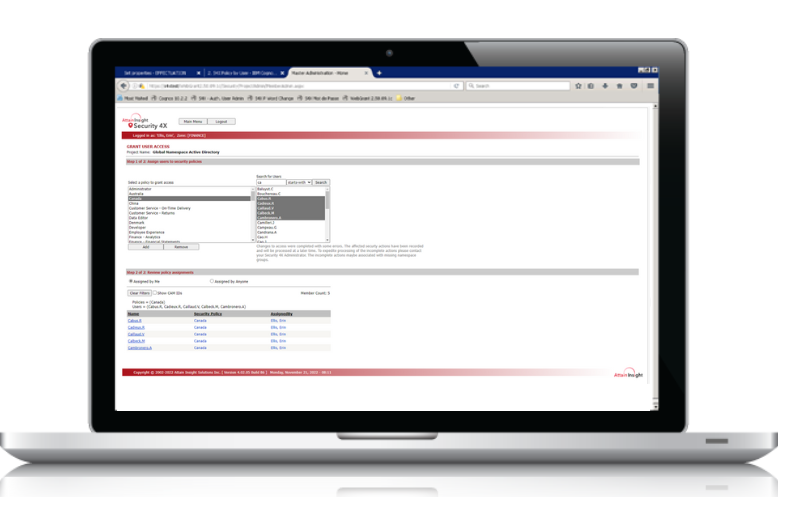
Attain Insight Security 4X™ allows you to streamline, automate, and scale security governance processes while simultaneously providing traceability and intelligent analytics that support a range of compliance objectives.
The entire Security 4X framework is designed to provide a rapidly provable audit and to streamline security processes by 90% or more. Security 4X will save your team time and money, and improve outcomes through a more reliable way to implement security.
The security management challenge for compliance and security in most organizations is ultimately focuses on two areas: Identity Provider (IdP) Directory Services integration and business applications that provide access to data, information and derivative content. The picture of who has access to what, and who approved access, and to what, necessarily links business applications with the IdP Directory Services that define and validate who each user is.
Security 4X is a centralized security administration and compliance management solution, built to handle complex enterprise security requirements for Apache LDAP, Google Identity Services, HCL Domino Directory, NetIQ eDirectory, Microsoft Active Directory and Okta.
For business analytics applications such as IBM Cognos Analytics, Security 4X provides a Compliance and Access Control solution for data and content, that utilizes Attain Insight’s leading access control technology.
Attain Insight’s compliance and security administration platform leverages a scalable multi-processing Role Based Access Control (RBAC) architecture with a Policy-based access control (PBAC) core. In addition to Attribute based access control (ABAC) Attain Insight has also made advancements with non-blocking Separation of Duty (SOD) capabilities and Dimensional access control, making the Security 4X platform one of the most advanced star-BAC solutions available anywhere.
Leading security solution that provides high performance attribute-based access control (ABAC) and attribute key based access control (AKAC) with optional key encryption (EAKAC). AKAC is required in high performance access control solutions and EAKAC is often required in shared or distributed security applications. Access is granted or denied based on a matrix of attributes values such as role, seniority, clearance, geography, division, project or any combination or part combination, or any other enterprise, software or user attributes. Attain Insight has been providing its advanced access control capabilities to organizations globally for a wide variety of use cases over more than two decades.
Changes to attribute values, security policy definitions or policy memberships is managed automatically and dynamically across complex system landscapes and topologies with full auditing built in. This achieves distributed, real-time security updates are correctly propagated to all target systems and software applications and data repositories.
Managing security across IdP directory services and business applications has its complexities. Security 4X provides a common control point for each. If you are migrating from one environment to another, Security 4X has tools to streamline your migration processes.
Provides IT with an ability to design “security policies” that drive governance
Allows IT to offload authorization processes to business users in a controlled manner through a web-based interface
Insulates IdP directory services from manual changes through a security engine that processes all security changes.
Allows IT to establish a security authorization baseline before carrying out mass changes
Allows IT to completely wipe away, rebuild, and migrate security from one geography, platform, or tier to another
Provides full logging and reporting of mass changes so that corporate audit standards are always maintained.
Comes with 25+ reports at multiple levels of granularity.
Tracks all security changes across time and provides a full audit trail.